I used to recommend LastPass. I stopped in late 2022 when the breach details came out. I am writing this now because people are still losing cryptocurrency in 2026 from credentials they stored before August 2022, and most of them have still not received a direct warning from the company.
When the breach news dropped, I did not panic immediately, but it definitely shook my confidence. A password manager is supposed to be the one thing you do not have to worry about. Even if the technical details say encrypted vaults were safe, the trust factor takes a hit. That part is hard to rebuild. And as the months went on and the theft reports started coming in, it became clear the technical details were not as reassuring as LastPass had implied.
In August 2022, attackers compromised a developer’s laptop at LastPass and walked out with source code. That was the first incident. In the second incident, using credentials from the first, they installed a keystroke logger on the personal laptop of a senior DevOps engineer in the United States, captured his credentials, and used them to download the full customer vault backup from Amazon S3.
What was stolen: usernames, passwords, and Secure Notes, every customer’s name, email address, billing address, and the website URLs stored in every vault entry.
Those unencrypted URLs meant attackers could identify every account linked to Coinbase, Kraken, Ledger, or any crypto platform before cracking a single password. They already knew which vaults were worth targeting.
What LastPass Said vs. What the ICO Found
On August 25, 2022, LastPass told users: “We have seen no evidence that this incident involved any access to customer data or encrypted password vaults.”
On September 15, 2022, after an investigation with Mandiant, LastPass said the attacker’s activity “was limited to a four-day period in August 2022” with “no evidence of access to customer data.”
The UK Information Commissioner’s Office later confirmed that LastPass had been “unable to determine” the full scope of the first incident because the attacker used anti-forensic techniques, and the investigation coincided with a scheduled macOS upgrade on the compromised device. They could not tell how bad it was. They told users nothing was wrong.
In December 2022, LastPass said the stolen vaults were encrypted and customers following best practices were protected.
The ICO investigated, issued a monetary penalty of £1,228,283 on November 20, 2025, and confirmed the breach was caused by a BYOD (bring your own device) policy failure. An employee was using a personal laptop to access production systems. There were no adequate controls on that device. The ICO found that LastPass failed to implement appropriate technical and organisational security measures under Articles 5(1)(f) and 32(1)(f) of the UK GDPR.
This was not a sophisticated nation-state attack. It was a policy gap.

Why the Vaults Are Being Cracked in 2026
The encryption on the stolen vaults is AES-256. That part is fine. The problem is how the encryption key is derived from the master password.
LastPass uses PBKDF2-SHA-256 to derive the vault encryption key from the user’s master password. The number of iterations determines how long each password guess takes to compute. More iterations means slower cracking.
Here is the iteration history for LastPass accounts:
| Account created | Default iterations | RTX 4090 guesses per second |
| Before 2018 | 5,000 | ~1,750,000/second |
| 2018 onwards | 100,100 | ~88,000/second |
| Current recommendation | 600,000 | ~15,000/second |
LastPass raised the default from 5,000 to 100,100 iterations in 2018. They did not retroactively update existing accounts. Security researcher Wladimir Palant flagged this to LastPass via Bugcrowd in February 2018. It was acknowledged. Nothing was done for four years.
At the time of the 2022 breach, a large share of legacy accounts still had 5,000 iterations. Some users who checked after the breach found their accounts set to 500 iterations. One person found 1 iteration.
At 5,000 iterations on an RTX 4090, a typical 10-character master password can be cracked in hours, not years.
LastPass’s December 2022 statement said accounts following best practices “would take millions of years to crack.” That is true for a current, strong, randomly generated master password at 600,000 iterations. It is irrelevant for a legacy account at 5,000 iterations, or for any user whose master password appeared in a previous breach database. The attackers check that database first, before they start guessing.
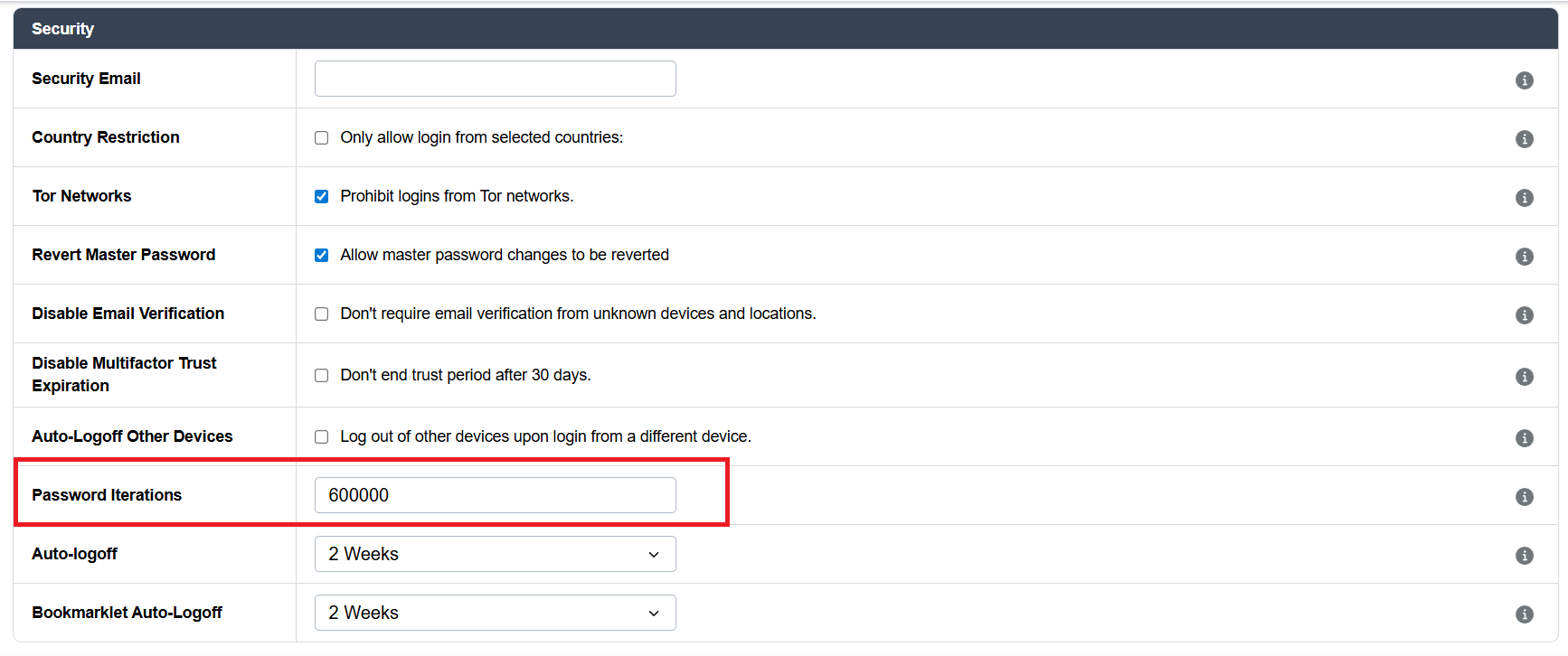
You can check your own iteration count. Go to Account Settings > Show Advanced Settings > Password Iterations. If you are a legacy user and that number is below 600,000, update it. This does not protect the vault backup that was already stolen in 2022. The attackers have that copy at the old iteration count. But it protects your account going forward.
The Money: $250 Million Estimated, Still Climbing
The theft has not stopped. Here is what has been confirmed:
| Period | Amount | Source |
| October 2023 | $4.4 million | On-chain analysis, multiple researchers |
| January 2024 | $150 million | Chris Larsen, Ripple co-founder; FBI confirmed the LastPass link |
| February 2024 | $6.2 million | SafetyDetectives |
| December 2024 | $12.38 million | Binance |
| Through late 2025 | $35 million total traced | TRM Labs |
| Total estimated (May 2024) | $250 million | Security Alliance |
| Total estimated (mid-2025) | $438 million | Blockchain researchers |
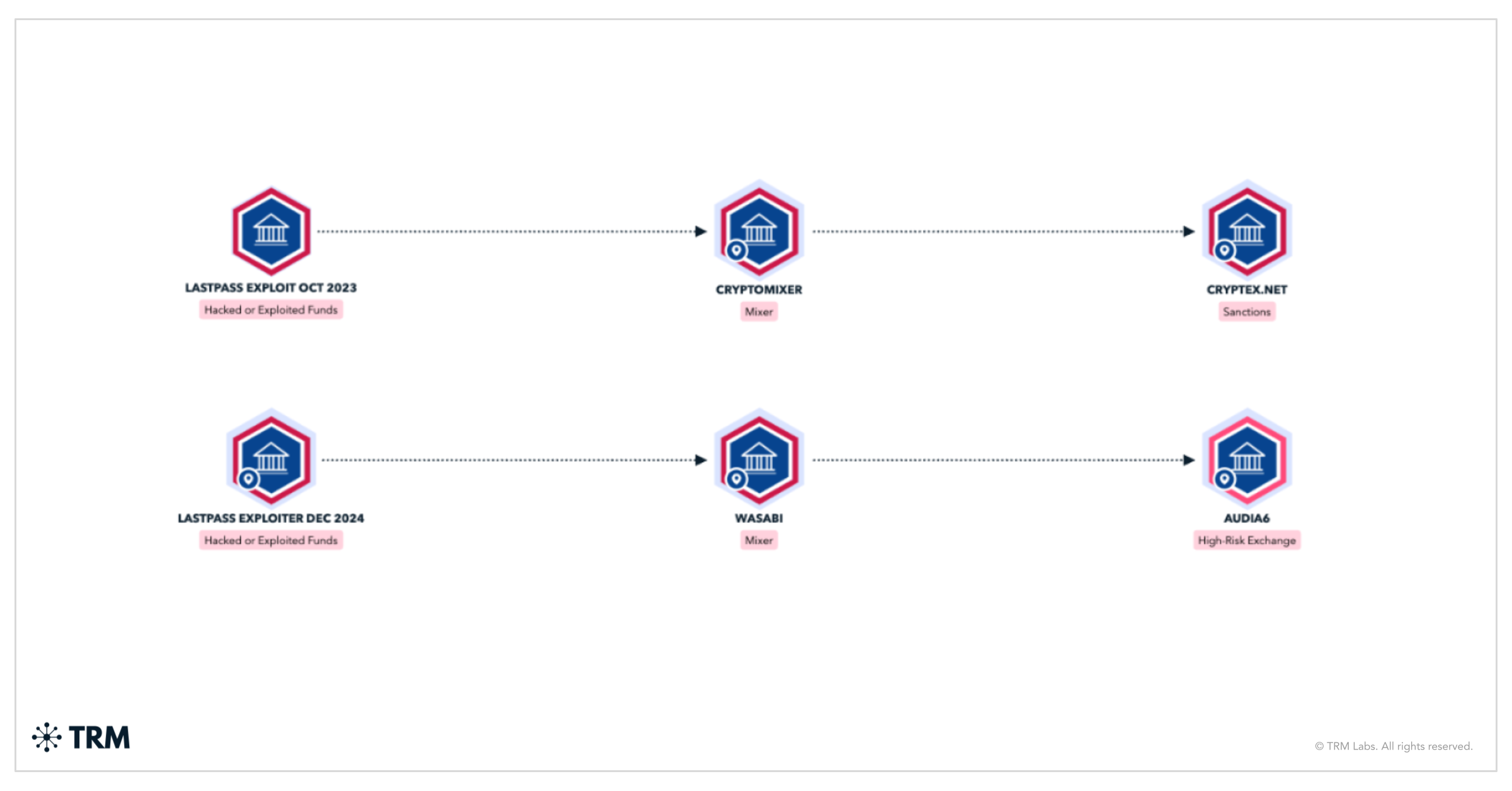
TRM Labs traced stolen funds to Russian exchanges including Cryptex, which the US Treasury sanctioned in 2024 for receiving $51.2 million in ransomware proceeds. Blockchain investigator ZachXBT documented that attackers group multiple victims together, routing funds through shared destination wallets before further laundering.
In March 2025, US authorities seized $23 million in stolen cryptocurrency, with court documents confirming FBI involvement.
In February 2026, it was confirmed that LastPass settled a class action for $24.5 million, with $16 million of that specifically allocated for cryptocurrency theft losses. The attorneys argued that LastPass had notice of the iteration count problem and failed to act.
LastPass’s public response in March 2025, after the FBI seizure: “We have been cooperating with law enforcement since we first disclosed this incident in 2022.”
No direct email to users about Secure Notes. No specific guidance on rotating crypto credentials. Three years later.
Secure Notes Problem
LastPass Secure Notes lets you store freeform text, SSH keys, software licenses, Wi-Fi passwords, and anything else that does not fit a standard password entry. Thousands of users stored cryptocurrency seed phrases, hardware wallet recovery phrases, and exchange API keys there.
All of it was in the stolen backup.
The encryption is only as strong as the master password and iteration count — for every reason covered above. A seed phrase stored in 2019 by a user with a legacy account at 5,000 iterations is exactly what the attackers are after.
As of April 2026, LastPass has not sent a targeted email to affected users saying: if you stored a seed phrase or private key in Secure Notes before August 2022, your funds are at risk. Move them now.
They updated their help pages. They published a general breach disclosure. They have not done the one thing that would reduce ongoing losses.
If you stored a seed phrase in Secure Notes before August 2022: move your crypto to a wallet derived from entirely new seed phrases before doing anything else. Do not just change your LastPass master password. The attackers have the old backup. Rotating your current credentials does not affect what they already have.
Who Owns LastPass Now
LastPass was founded in 2008. GoTo (formerly LogMeIn) bought it for $110 million in 2015. In 2020, Francisco Partners and Elliott Management, two private equity firms, took GoTo private. In May 2024, they spun LastPass out under a holding entity called LMI Parent, L.P.
Francisco Partners also owns or has owned Barracuda Networks and SolarWinds. Elliott Management manages $70 billion in assets.
The pricing record under this ownership: Premium personal pricing has gone from $12/year (2015) to $36/year today. The pricing tier structure has been changed six times between July 2024 and February 2026. Contracts auto-renew at full non-discounted rates and cannot be downgraded mid-term.
There is no warrant canary on LastPass’s transparency page. No public record of how many government data requests the company receives. The company operates under US law.
What Real Users Are Reporting
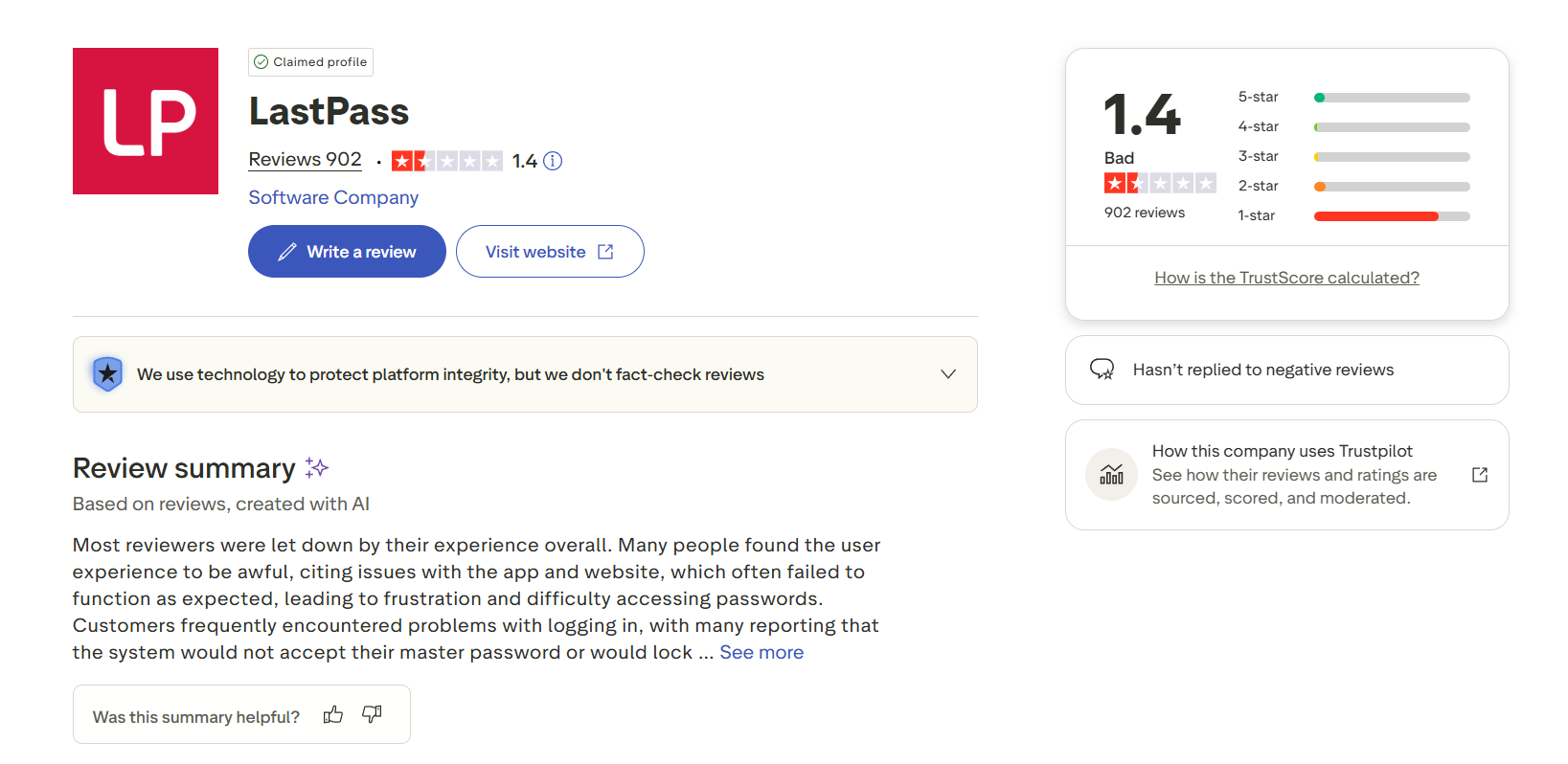
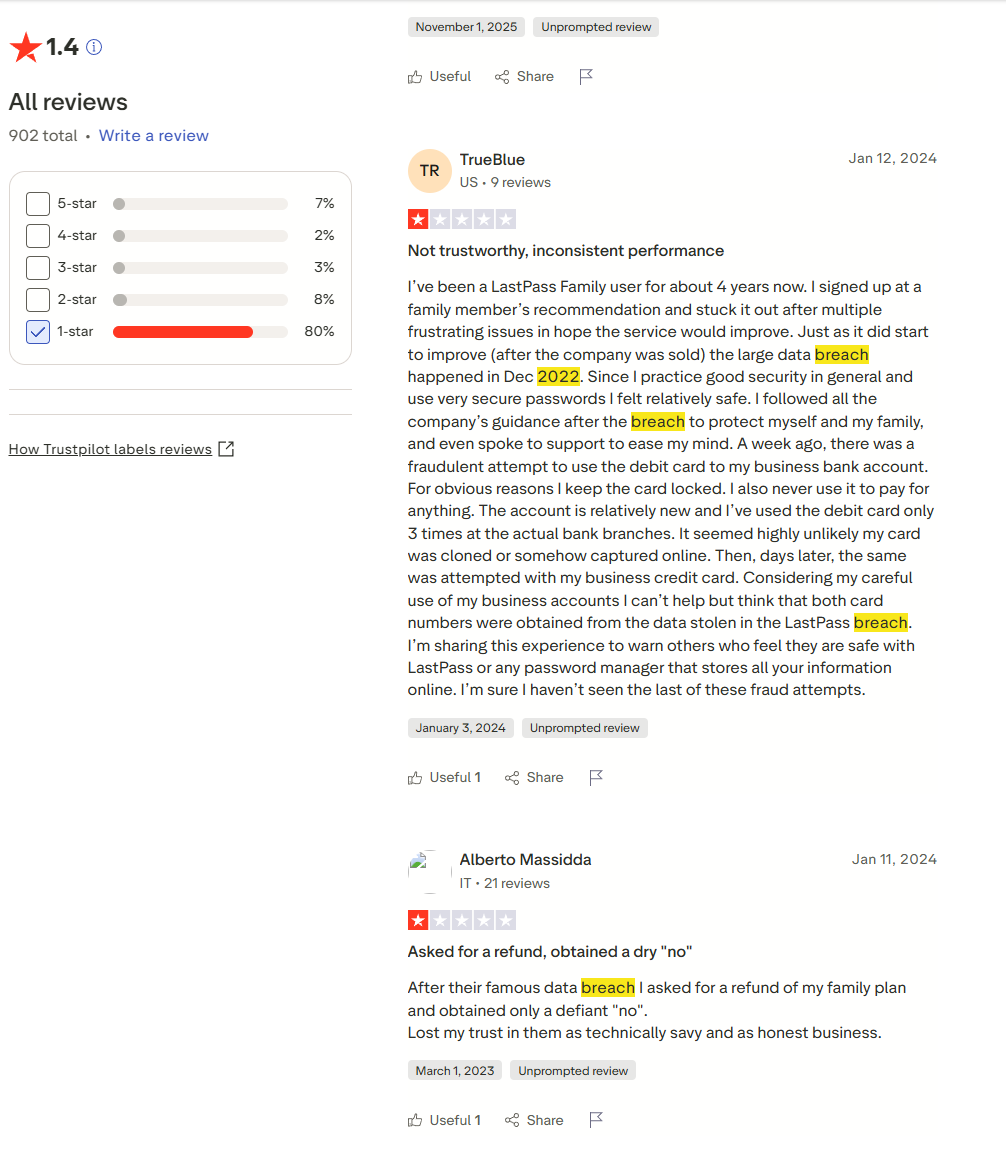
TrustPilot has 897 LastPass reviews as of April 2026. The distribution is heavily negative. Below are the patterns that appear repeatedly, not isolated complaints.
Charges after cancellation. Multiple users describe completing the cancellation steps inside the LastPass app and being charged on their renewal date. LastPass support’s documented response in several cases: the user had a “different type of subscription” requiring a different cancellation process. One ConsumerAffairs reviewer filed a fraud claim with their credit card issuer after two consecutive years of attempted cancellation.
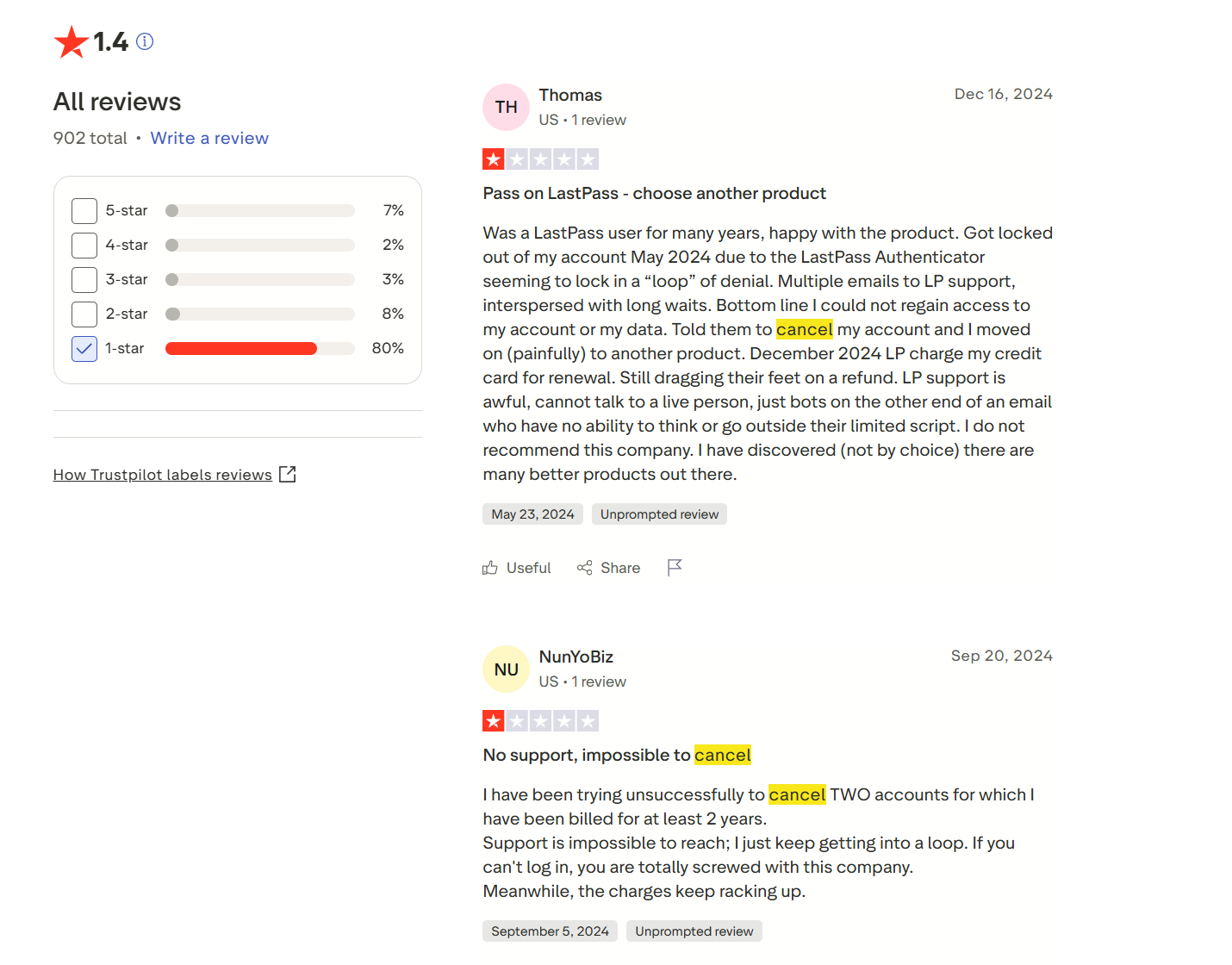
Locked out with no reachable support. After changing phones, updating the LastPass Authenticator app, or triggering a security flag, users describe permanent lockout with no working recovery path. Personal plans include no live chat. One TrustPilot reviewer submitted four responses to a support ticket (case number #02847588, visible in their public review) and received automated replies saying they had not responded. The self-help guides reference interface versions that no longer exist.

iOS Safari autofill does not work. TrustPilot, ConsumerAffairs, and Reddit contain consistent reports of the same iOS Safari behavior: tapping the autofill prompt opens the LastPass app instead of filling the field in place. One ConsumerAffairs reviewer described it as “a black hole of user experience” that has been present for so long that users treat it as normal. Not fixed as of Q1 2026.
No breach guidance from the company. A share of low-star reviews directly mention 2022. Users describe not knowing which credentials are still at risk and not receiving direct communication about Secure Notes. One TrustPilot reviewer wrote that they “survived the data breaches (I hope)” after finding a broken 2FA setup in 2025. The company has the email addresses of every affected user. They have not used them to send a targeted warning.
What I Use Instead
Most people switching away from LastPass are going to Bitwarden, and there is an obvious reason: it is free. Not a limited free tier with device restrictions like LastPass.
Actually free, across all devices, platforms, and browsers, with no features locked behind a paywall for everyday use. It does everything most people need a password manager to do. It is open-source, which means the security model can be verified by anyone, not just taken on faith. Cure53 audited it in 2022 and found no critical issues. If you stored no crypto credentials in LastPass before August 2022 and want to switch today without spending anything, Bitwarden is where you go.
I personally user Keeper. I have been using it as my primary password manager for the past 3 years. No breach history. Independent SOC 2 Type II audit. Personal plan costs $34.99/year, which is comparable to what LastPass Premium costs.
If you want the strongest architecture against the specific attack vector that compromised LastPass, 1Password derives the vault encryption key from a combination of your master password and a Secret Key, a 128-bit string stored locally and never transmitted. A stolen vault backup is useless without it. $35.88/year for individuals.